What is quantum encryption technology? At its most fundamental, QET represents the very leading edge of data encryption science. Data encryption science, in turn, affects every single person on this planet. It is all that stands between the most private, sensitive data and the hackers who want to obtain it.
As fast as data encryption technology advances, processes to decrypt it advance likewise – an escalating data war some sources are now calling the “quantum arms race.” And yet this term fits for reasons that are well understood and also reasons that are not so well understood.
Luckily, it is not necessary to have a degree in physics or mathematics to harness the power of emerging technology. It is only necessary to understand that it exists, grasp the basics of how it works and apply it for your personal and commercial data protection needs.
Quantum Cryptography Defined
As a term, “quantum cryptography” is a mouthful. To further confuse matters, the similar terms “quantum cryptology,” “quantum encryption,” “quantum key encryption” and additional variations thereof are used almost interchangeably to describe the exact same processes.
So what exactly does quantum cryptography mean?
Quantum Defined
Even though quantum as a term is associated with high-level physics, mechanics, engineering and mathematical principles, at its most fundamental the word quantum simply means limited.
In other words, quantum as a term defines a finite amount of something, whether it be atoms, light photons, electrons, money, data or something else.
As a point of reference, the word quantum is most closely associated with the field of quantum mechanics, which is the science of explaining how such tiny particles behave throughout the universe.
Cryptography Defined
The word cryptography means code-writing and/or code-solving (code-breaking). Encryption is a form of code-writing. Decryption is a form of code-solving or code-breaking.
Quantum Cryptography Defined
Putting these two terms together, what emerges is a description of how to use very small particles – in this case light photons – to carry equally small bits of data securely from Point A to Point B. Sounds simple enough, right? It is just a bit more complicated than that, as you have likely already guessed.
How Quantum Cryptography Works with Data Transmission
Let’s say there is a data package that needs to be securely transmitted using quantum encryption technology. The data itself is prepared by the sender at Point A to be transmitted to the receiver at Point B.
Once the data package is ready, it is time to encrypt and transmit it. Each data bit will be attached to a light photon – sort of like a micro-bundle on top of its own micro-camel. All the data bits and their light photons are lined up and ready to send.
As the light photons and their data bit passengers take off from Point A, they each pass through a polarizing filter. This polarizing filter randomly assigns each traveling photon a certain degree of polarization, of which four types exist. Neither photons nor their sender knows which of the four degrees each photon will receive.
Once the convoy of light photons and their data bit passengers reach Point B, they pass through another type of filter called a polarization decoder, also called a receiver or beam splitter. This beam splitter can figure out which of the four types of polarization each photon/data bit has been given.
And here is the most important part: this beam splitter is only looking for certain types of polarization. So it picks out which photons/data bits have been assigned the relevant type(s) of polarization and basically trashes the other photons/data bits.
The photons and data bits that remain become what is called the “data key” or simply the key. The key is what is used to decrypt the data – detaching the data bits from their light photons so the data can be received, read and used as needed.
But before the key is generated, the beam splitter also compares whether the relevant photons/data bits have been compromised by exposure to any other beam splitters (decryption tools) along their journey from Point A to Point B. Those photons that have been so exposed will be altered in detectable ways.
When alteration is detected, this means the data security has been compromised. No key is generated, both the sender and the receiver are alerted to the attempt and it is back to square one. A new data set must be transmitted and a new key must be generated before the receiver can view and use the data being sent.
Quantum Cryptography in the Age of Quantum Computers
The reason why quantum encryption technology is so vitally relevant today is perhaps best understood from the perspective of advances in computer technology itself.
Most everyone has seen a movie depictions of quantum computers – whole rooms of massive machines that are often strung together with cables, with the whole system busy doing what computers do – working out the most complex mathematical equations on earth.
But just as the first mobile phones were the size of today’s smart tablets, so too are quantum computers getting smaller by the year. At some point in what now appears to be the not-so-distant future, quantum computers could be both small enough and affordable enough for mainstream access.
When this occurs (and it truly is a matter of when, not if) it will make vulnerable the vast majority of the most sensitive, high-level data held by institutions across the planet – from banks and credit unions to government and military facilities. Certainly private personal data will be easy to access, use and misuse when this occurs.
Future Outlook for Quantum Cryptology
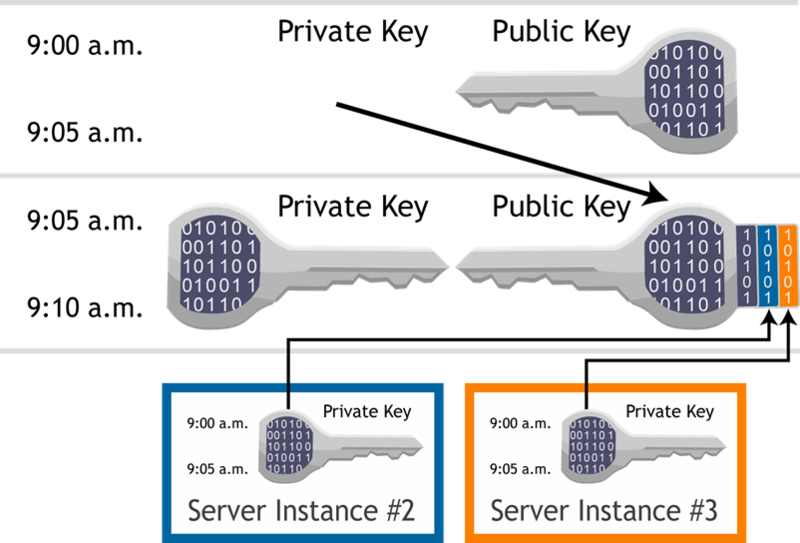
Using the same public key encryption technology that has been in use for decades is no longer a feasible strategy looking forward.
Peering into the future of data encryption reveals that quantum key distribution (QKD), a function of quantum cryptology itself, is the next step forward to continue securing sensitive data.
This is not to say there will not still be windows of opportunity that hackers could potentially explore and exploit. But there has already been advancement towards what may just be a truly unbreakable QKD process – and this wraps in the use of satellite technology to avoid fiber optic cable relays over long distances.
Up ahead in the distance is quantum entanglement, which uses mirror photons to secure data from end to end in a way that any attempted access by a third party will disable on the spot.
But for the moment, quantum cryptology can still feel a bit too esoteric for mainstream consumption, and this is not an invalid assessment. The day is coming when QKD technology will be available to replace traditional public key encryption. The goal is to ensure QKD technology arrives before quantum computers do!